Daily Cyber Threat Report | Australia – Japan – Asia | 23 April 2026
Executive Summary (BLUF)
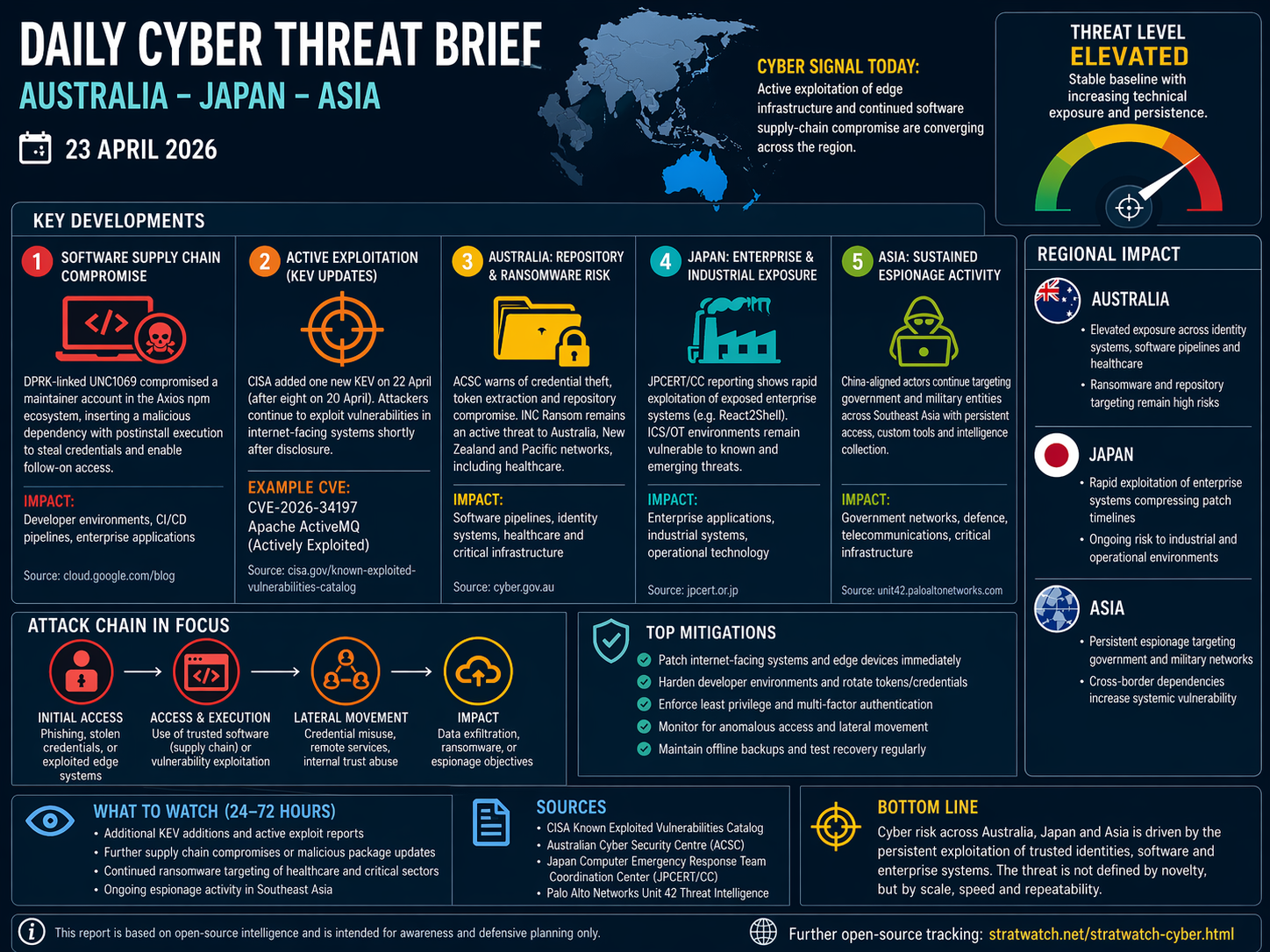
Today’s Indo-Pacific cyber threat environment is defined by the convergence of edge exploitation, software supply-chain compromise, and identity-driven access operations. Recent activity—spanning DPRK-linked package compromise, continued additions to the Cybersecurity and Infrastructure Security Agency Known Exploited Vulnerabilities (KEV) catalogue, Australian reporting on repository targeting and ransomware, and persistent China-aligned espionage—indicates that attackers are prioritising trusted systems and scalable access pathways over bespoke or novel techniques.
The central judgement is that risk is cumulative. Attackers are repeatedly exploiting the same trust relationships—software dependencies, credentials, and exposed infrastructure—to sustain access across multiple sectors. This creates systemic vulnerability across Australia, Japan, and the broader Asian region.
Operating Environment
The threat baseline remains stable, but technical exposure is increasing in both speed and breadth.
Recent KEV updates from Cybersecurity and Infrastructure Security Agency (20–22 April) confirm that vulnerabilities in enterprise and edge systems continue to be actively exploited shortly after disclosure. This reflects a persistent trend: exploit timelines are now measured in days rather than weeks.
At the same time, Australian Cyber Security Centre reporting continues to highlight two structurally important pressures:
Targeting of online code repositories and developer ecosystems
Ongoing ransomware activity affecting healthcare and regional networks
Across Asia, reporting from Palo Alto Networks Unit 42 reinforces the persistence of China-aligned espionage activity focused on government and military entities, marked by long-term access and tailored intelligence collection.
Key Developments
Software Supply Chain Compromise (Axios / DPRK-linked activity)
Recent reporting attributes compromise of the Axios npm package ecosystem to DPRK-linked actor UNC1069.
Tactics, Techniques, and Procedures (TTPs):
Compromise of maintainer accounts
Insertion of malicious dependencies into trusted packages
Use of postinstall scripts for execution
Credential harvesting from downstream environments
Systems Targeted:
npm package ecosystem
Developer workstations and CI/CD pipelines
Enterprise applications using affected dependencies
Why it matters:
This is a high-impact example of trusted software exploitation at scale. A single compromised dependency can propagate across thousands of environments, bypassing traditional perimeter controls.
Active Exploitation of Known Vulnerabilities (KEV updates)
CISA’s KEV updates on 20–22 April confirm continued exploitation of enterprise and edge vulnerabilities.
TTPs:
Automated scanning of internet-facing systems
Exploitation of recently disclosed CVEs
Deployment of web shells and remote access tools
Systems Targeted:
Web applications and APIs
VPNs and remote access infrastructure
Cloud-hosted enterprise services
Why it matters:
The key issue is patch compression. Organisations with limited asset visibility or slower patch cycles are increasingly exposed.
Australia: Repository Targeting and Ransomware Activity
Australian Cyber Security Centre continues to warn of targeting of code repositories, alongside ongoing activity by INC Ransom.
TTPs:
Credential theft and token extraction
Access to private repositories
Privilege escalation via administrative accounts
Lateral movement across enterprise networks
Data exfiltration and double extortion
Systems Targeted:
Git repositories and development pipelines
Active Directory and enterprise identity systems
Healthcare and critical infrastructure systems
Why it matters:
This activity highlights the overlap between software supply chain compromise and ransomware operations, reinforcing identity and trust as central vulnerabilities.
Japan: Enterprise and Industrial System Exposure
Japan Computer Emergency Response Team Coordination Center reporting continues to highlight rapid exploitation of enterprise vulnerabilities (e.g., React2Shell), alongside a sustained focus on industrial control system (ICS) security.
TTPs:
Rapid exploitation of newly disclosed vulnerabilities
Deployment of remote access tools and persistence mechanisms
Opportunistic compromise of exposed systems
Systems Targeted:
Public-facing enterprise applications
Industrial control systems and operational technology
Cloud-connected enterprise environments
Why it matters:
Japan’s risk profile is defined by compressed patch timelines and exposure of operational systems, increasing the likelihood of rapid compromise.
Asia: Sustained China-Aligned Espionage Activity
Reporting from Palo Alto Networks Unit 42 highlights continued China-aligned activity targeting government and military entities across Southeast Asia.
TTPs:
Long-term persistence within networks
Dormant access and delayed execution
Credential harvesting and lateral movement
Custom malware and backdoors
Systems Targeted:
Government networks
Military and defence systems
Telecommunications and critical infrastructure
Why it matters:
This reflects strategic intelligence collection and preparation of the cyber environment, rather than immediate disruption.
Technical and Tradecraft Observations
Identity as the Primary Attack Surface
Across all reporting, compromised credentials and tokens remain the dominant entry point. Active Directory, cloud identity systems, and API tokens are central to both access and persistence.
Trusted Software as a Force Multiplier
Supply chain compromise (Axios) and repository targeting demonstrate that attackers are leveraging trusted software ecosystems to scale access across multiple organisations.
Exploit Velocity and Patch Compression
KEV updates and rapid exploitation cases reinforce that vulnerability exploitation is accelerating, reducing effective defensive timelines.
Lateral Movement and Privilege Escalation
Ransomware activity continues to rely on:
Administrative account creation
Remote service abuse
Internal trust exploitation
Convergence of Tradecraft Across Actors
State and criminal actors are increasingly using the same techniques. The distinction between them is increasingly defined by intent rather than capability.
Regional Implications
Australia
High exposure across software pipelines, healthcare, and identity systems
Increasing overlap between supply chain compromise and ransomware
Japan
Elevated risk from rapid exploitation of enterprise systems
Continued vulnerability in industrial and operational environments
Asia
Persistent espionage targeting government and military systems
Regional interconnectivity amplifying systemic risk
Strategic Assessment
The Indo-Pacific cyber environment is defined by convergence at the level of access and trust. Attackers are exploiting the same systems—identity platforms, software pipelines, and edge infrastructure—to achieve different objectives.
This suggests ongoing preparation of the cyber environment, where access is established and maintained for future use. The result is a risk landscape characterised by cumulative degradation of resilience, rather than isolated incidents.
Outlook (24–72 Hours)
Key watchpoints:
Additional KEV entries and exploitation alerts
Further supply chain compromise reporting
Continued ransomware activity in healthcare and critical sectors
Ongoing espionage targeting regional government networks
Bottom Line
Cyber risk across Australia, Japan, and Asia is being driven by the persistent exploitation of trusted identities, software, and enterprise systems. The threat is not defined by novelty, but by the scale and repeatability of these access pathways.
Methodology / Sources
Cybersecurity and Infrastructure Security Agency
Australian Cyber Security Centre
Japan Computer Emergency Response Team Coordination Center
Palo Alto Networks Unit 42
Confidence
Moderate to High — based on consistent reporting across multiple authoritative sources and aligned threat patterns.