Daily Cyber Threat ReportAustralia – Japan – Asia 29 April 2026
Executive Summary
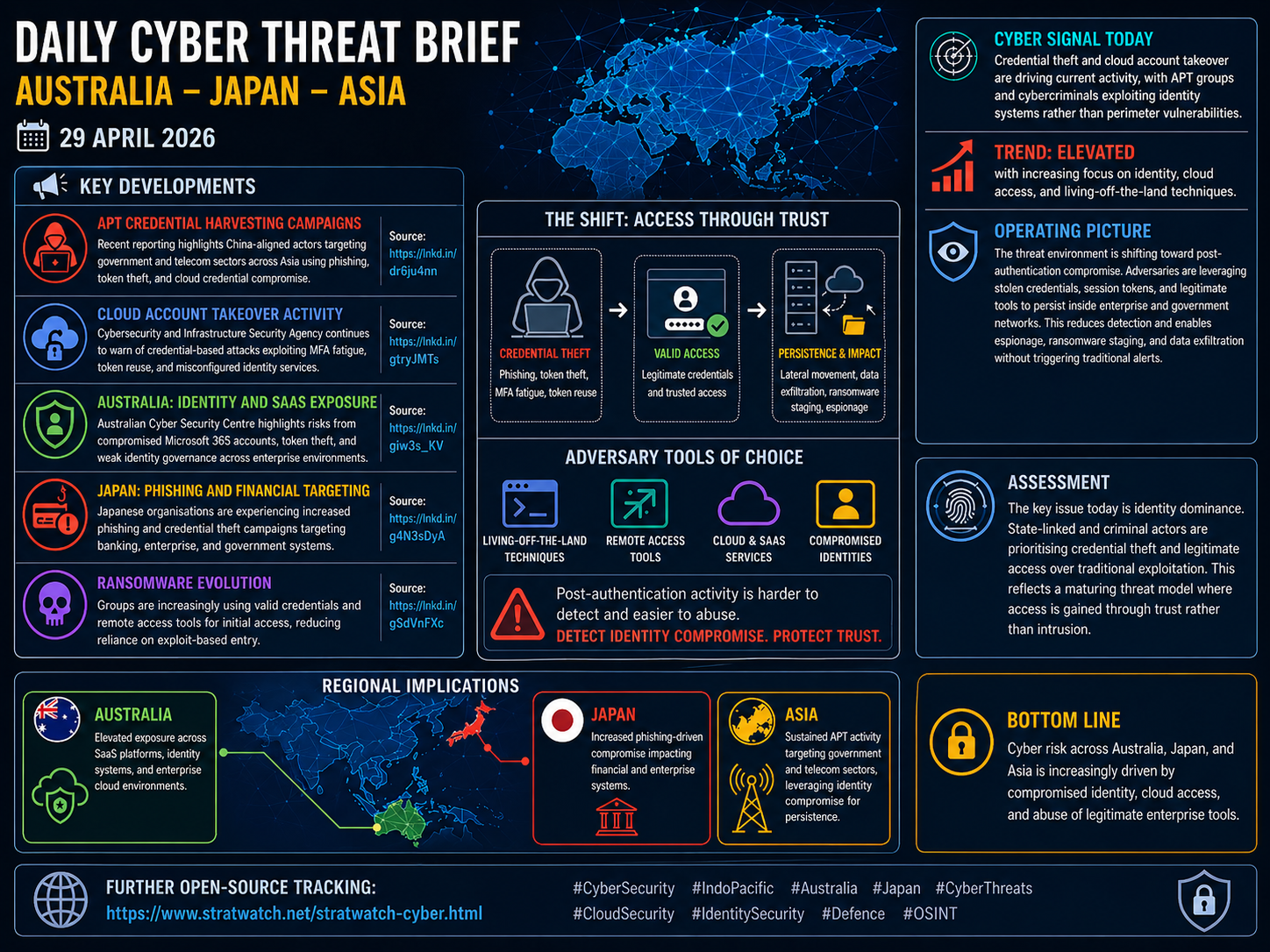
Cyber activity across the Indo-Pacific continues to demonstrate a decisive shift toward identity-driven compromise. Both state-aligned actors and cybercriminal groups are prioritising credential theft, session hijacking, and abuse of legitimate access pathways over traditional vulnerability exploitation.
The operational environment is increasingly defined by post-authentication activity. Adversaries are gaining access through phishing, token theft, and identity misconfigurations, then operating within trusted systems using legitimate tools. This reduces detection, extends dwell time, and enables espionage, ransomware staging, and data exfiltration with minimal forensic footprint.
The threat level remains elevated, with identity systems now representing the primary attack surface.
Threat Environment Overview
Three interrelated dynamics are shaping the current threat landscape:
Identity as the primary attack vector: Credentials, tokens, and authentication workflows are now the central focus of intrusion activity.
Post-authentication operations: Attackers are bypassing perimeter controls and operating within environments using legitimate accounts and tools.
Convergence of espionage and cybercrime: Techniques used by APT groups and ransomware operators are increasingly aligned, particularly in credential harvesting and access persistence.
This reflects a mature threat model in which the objective is not entry, but sustained, low-visibility access.
Key Developments
APT Credential Harvesting Campaigns
Recent reporting indicates China-aligned actors are conducting credential harvesting operations targeting government and telecommunications sectors across Asia. Techniques include phishing campaigns, session token theft, and compromise of cloud-based identity systems.
Assessment:
These campaigns are consistent with long-term access operations rather than opportunistic intrusion. The targeting of identity systems enables persistence across multiple environments and reduces reliance on repeat exploitation.
Cloud Account Takeover Activity
The Cybersecurity and Infrastructure Security Agency continues to highlight credential-based attacks exploiting MFA fatigue, token reuse, and poorly configured identity services. Attackers are leveraging social engineering and authentication weaknesses to gain persistent access to cloud environments.
Assessment:
Multi-factor authentication is being systematically degraded as a defensive control through user manipulation and token theft. Organisations relying on MFA as a standalone safeguard are increasingly exposed.
Australia: Identity and SaaS Exposure
The Australian Cyber Security Centre has identified ongoing risks associated with compromised Microsoft 365 accounts, token theft, and weak identity governance across enterprise and government environments.
Assessment:
Australia’s reliance on SaaS platforms introduces systemic risk where identity controls are insufficient. Visibility gaps across federated identity systems and third-party integrations remain a key vulnerability.
Japan: Phishing and Financial Targeting
Japanese organisations are experiencing a sustained increase in phishing campaigns targeting banking institutions, enterprise systems, and government entities. These campaigns are designed to harvest credentials and facilitate downstream financial and data exploitation.
Assessment:
The financial sector remains a high-value target due to direct monetisation opportunities. The persistence of phishing-driven compromise indicates that user-layer defences remain insufficient.
Ransomware Evolution Toward Valid Access
Ransomware groups are increasingly relying on valid credentials and remote access tools for initial access. This reduces dependence on exploit-based entry and aligns their tradecraft with APT-style operations.
Assessment:
This evolution reflects a shift toward stealth and efficiency. Credential-based access allows ransomware actors to bypass security controls and accelerate lateral movement within networks.
Primary Attack Vectors
Credential harvesting (phishing, token theft, session hijacking)
Cloud account takeover (MFA fatigue, token reuse, identity misconfiguration)
Abuse of legitimate tools (living-off-the-land techniques)
Remote access exploitation using valid credentials
Data exfiltration via authorised channels and cloud services
Regional Assessment
Australia
Elevated exposure across Microsoft 365 and SaaS ecosystems
Identity governance and access control weaknesses remain a critical issue
Increased risk of data exposure through compromised enterprise accounts
Japan
Persistent phishing activity targeting financial and enterprise sectors
Credential theft driving both financial crime and network compromise
Industrial and enterprise continuity increasingly exposed to identity-based intrusion
Asia (Broader Region)
Sustained APT activity targeting government and telecommunications sectors
Identity compromise enabling long-term persistence and intelligence collection
Shared reliance on cloud and SaaS platforms amplifying regional risk
Outlook (24–72 Hours)
Continued phishing campaigns targeting enterprise and government users
Further reporting of credential theft and cloud account compromise
Expansion of APT access operations leveraging stolen tokens
Increased ransomware activity using valid credentials and remote access tools
Additional advisories relating to identity system misconfigurations and exploitation
Mitigation Priorities
Implement phishing-resistant authentication, including hardware-based MFA where possible
Enforce strict identity governance, including least privilege and session management controls
Monitor for anomalous authentication activity, including token misuse and unusual login patterns
Harden cloud identity configurations, including conditional access policies
Restrict and audit remote access tools and administrative privileges
Improve user awareness and resilience against phishing and MFA fatigue attacks
Analyst Assessment
The current threat environment confirms that identity has become the central terrain of cyber operations. The distinction between intrusion and legitimate access is increasingly blurred, as adversaries operate through trusted credentials and authorised tools.
This presents a structural challenge for defence. Traditional detection models based on perimeter breaches and malware signatures are insufficient against adversaries who appear as legitimate users within the system.
Effective defence now depends on continuous validation of identity, behaviour, and access patterns rather than static authentication events.
Bottom Line
Cyber risk across Australia, Japan, and Asia is now driven primarily by compromised identity, cloud access, and the abuse of legitimate enterprise tools. Organisations that fail to secure identity systems will remain exposed regardless of perimeter strength.
Further open-source tracking:
https://stratwatch.net/stratwatch-cyber.html