Daily Cyber Threat Report | Australia – Japan – Asia | 24 April 2026
Executive Summary (BLUF)
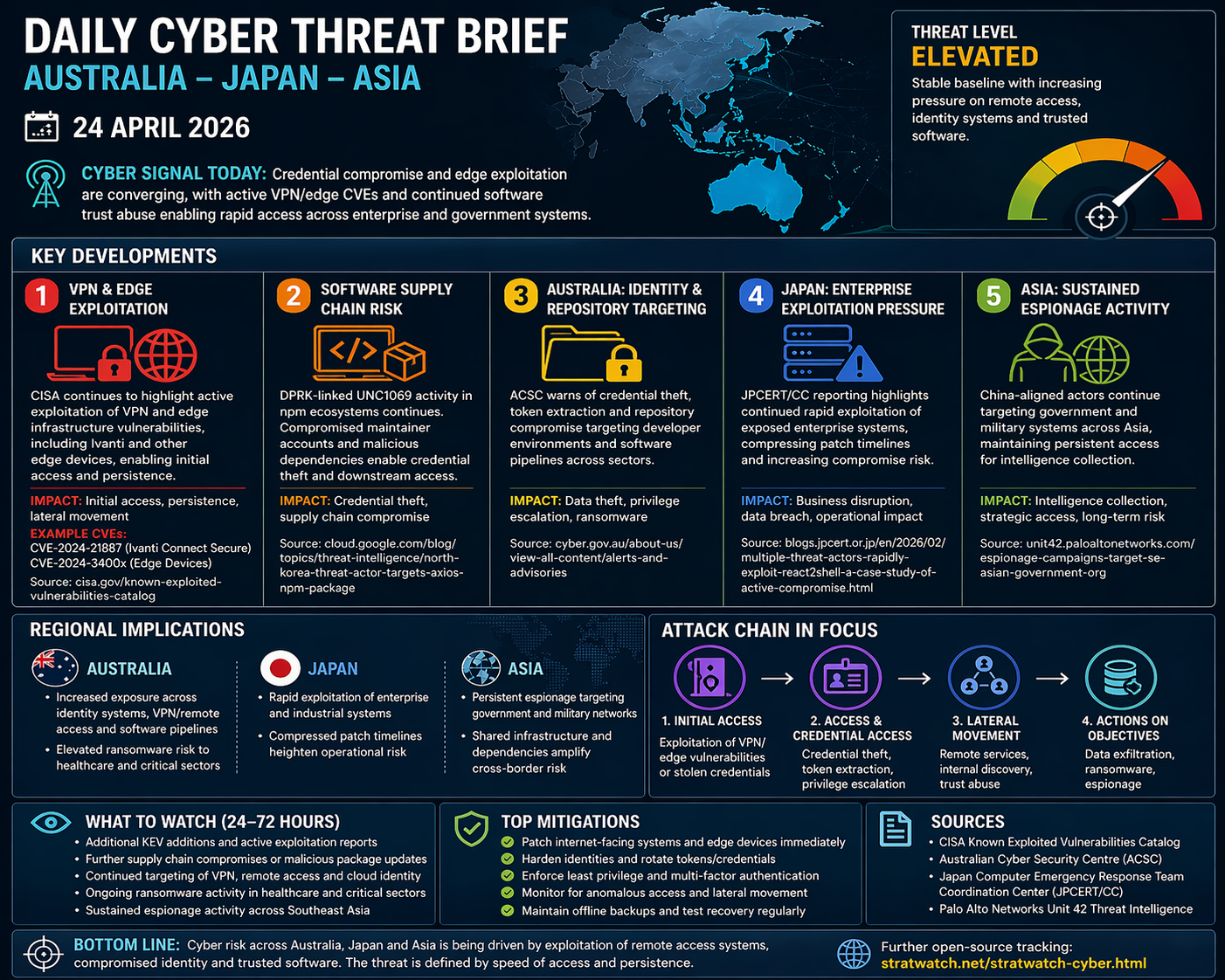
Today’s Indo-Pacific cyber threat environment is characterised by the convergence of remote access exploitation, identity compromise, and software supply-chain abuse. The strongest current signals include continued exploitation of VPN and edge infrastructure, ongoing supply-chain compromise activity linked to DPRK-aligned actors, sustained Australian reporting on repository and credential targeting, and persistent China-aligned espionage across Asia.
The central judgement is that attackers are increasingly prioritising remote access pathways and trusted identity systems as scalable entry points. This enables both state-linked intelligence collection and criminal operations, creating a threat environment defined by persistent access rather than isolated incidents.
Operating Environment
The overall threat baseline remains stable, but exposure is increasing at the network edge and identity layer.
Recent updates from Cybersecurity and Infrastructure Security Agency continue to highlight active exploitation of vulnerabilities affecting VPN appliances and edge infrastructure. These systems are particularly attractive because they provide direct access into enterprise networks and often sit outside traditional monitoring visibility.
At the same time, Australian Cyber Security Centre continues to report targeting of software development environments and credential stores, reinforcing that identity systems and software pipelines remain critical attack surfaces.
Across Asia, reporting from Palo Alto Networks Unit 42 indicates ongoing China-aligned activity targeting government and military entities, characterised by persistence, stealth, and tailored intelligence collection.
Key Developments
Active Exploitation of VPN and Edge Infrastructure
CISA reporting highlights continued exploitation of vulnerabilities affecting VPN appliances and edge devices, including Ivanti and similar remote access technologies.
Tactics, Techniques, and Procedures (TTPs):
Exploitation of known vulnerabilities in VPN and edge devices
Use of web shells and remote access tools
Establishment of persistence within edge infrastructure
Credential harvesting from authenticated sessions
Systems Targeted:
VPN appliances and remote access gateways
Edge devices and network infrastructure
Enterprise authentication systems
Why it matters:
These systems provide direct entry points into enterprise environments, making them highly valuable for both initial access and persistence.
Ongoing Software Supply Chain Compromise (DPRK-linked activity)
DPRK-linked actor UNC1069 continues to target npm ecosystems, leveraging compromised maintainer accounts and malicious dependencies.
TTPs:
Account takeover of package maintainers
Insertion of malicious code into trusted dependencies
Use of installation scripts for execution
Credential theft and environment reconnaissance
Systems Targeted:
npm and software package ecosystems
Developer environments and CI/CD pipelines
Enterprise applications relying on affected libraries
Why it matters:
Supply chain compromise enables scalable access across multiple organisations, bypassing traditional security controls.
Australia: Identity and Repository Targeting
Australian Cyber Security Centre continues to warn of targeting of online repositories and credential stores.
TTPs:
Phishing and social engineering for credential theft
Extraction of API tokens and secrets
Access to private repositories
Manipulation of software packages
Systems Targeted:
Developer platforms and repositories
Cloud identity systems
Enterprise applications and services
Why it matters:
This reflects a shift toward identity-driven compromise, where attackers target credentials rather than infrastructure.
Japan: Enterprise and Industrial System Exposure
Japan Computer Emergency Response Team Coordination Center reporting highlights continued rapid exploitation of enterprise systems, alongside ongoing concerns around industrial control systems (ICS).
TTPs:
Rapid exploitation of newly disclosed vulnerabilities
Deployment of persistence mechanisms
Opportunistic targeting of exposed systems
Systems Targeted:
Public-facing enterprise applications
Industrial control systems and operational technology
Cloud-connected environments
Why it matters:
Japan’s risk is driven by compressed patch timelines and exposure of operational systems, increasing the likelihood of rapid compromise.
Asia: Sustained China-Aligned Espionage Activity
Unit 42 reporting highlights ongoing China-aligned cyber activity targeting government and military systems across Southeast Asia.
TTPs:
Long-term persistence and stealth operations
Credential harvesting and lateral movement
Deployment of custom malware and backdoors
Targeted intelligence collection
Systems Targeted:
Government and defence networks
Telecommunications infrastructure
Critical systems supporting state operations
Why it matters:
This activity reflects strategic intelligence collection and preparation, not immediate disruption.
Technical and Tradecraft Observations
Identity as the Primary Attack Surface
Compromised credentials and tokens remain the dominant entry point across all activity, reinforcing identity systems as critical vulnerabilities.
Edge Infrastructure as a High-Value Target
VPNs and edge devices are increasingly exploited due to their direct access to enterprise networks and limited visibility.
Trusted Software as an Access Multiplier
Supply chain compromise continues to scale attacker access across multiple organisations via trusted dependencies.
Exploit Velocity and Patch Compression
Attackers are exploiting vulnerabilities rapidly after disclosure, reducing effective patch timelines.
Convergence of Tradecraft
State and criminal actors are using similar techniques, with differences driven by intent rather than capability.
Regional Implications
Australia
Elevated exposure across identity systems, remote access infrastructure, and software pipelines
Increasing overlap between supply chain compromise and ransomware
Japan
Continued risk from rapid exploitation of enterprise systems
Ongoing exposure in industrial and operational environments
Asia
Persistent espionage targeting government and military systems
Interconnected infrastructure amplifying regional risk
Strategic Assessment
The Indo-Pacific cyber threat environment is defined by convergence at the level of access and trust. Attackers are exploiting the same systems—VPNs, identity platforms, and software pipelines—to achieve different objectives.
This reflects ongoing preparation of the cyber environment, where access is established and maintained for future use. The cumulative effect is a gradual erosion of resilience across interconnected systems.
7. Outlook (24–72 Hours)
Key watchpoints:
Continued exploitation of VPN and edge vulnerabilities
Further supply chain compromise reporting
Ongoing ransomware targeting of healthcare and critical sectors
Sustained espionage activity across Asia
8. Bottom Line
Cyber risk across Australia, Japan, and Asia is being driven by exploitation of remote access systems, identity compromise, and trusted software. The threat is defined by persistence, scale, and repeatability.
9. Methodology / Sources
Cybersecurity and Infrastructure Security Agency
Australian Cyber Security Centre
Japan Computer Emergency Response Team Coordination Center
Palo Alto Networks Unit 42
10. Confidence
Moderate to High — based on consistent reporting across multiple authoritative sources and aligned threat patterns.